CMPUT 404
Web Applications and Architecture
Authentication
Created by
Abram Hindle
(abram.hindle@ualberta.ca)
and Hazel Campbell (hazel.campbell@ualberta.ca).
Copyright 2014-2023.
Web Authentication
- Authentication methods supported by Web Standards
HTTP Basic Auth
- Created by Ari Luotonen in 1993.
- Username and password not hidden by HTTP
- You must use another encryption layer (TLS) below HTTP (HTTPS) for security!
HTTP Basic Auth
- Easiest to implement
- Stateless
- Response:
401 Unauthorized&WWW-Authenticate: Basicheader. - Request:
Authorization: Basicheader
HTTP Basic Auth
- The username and password are encoded but not encrypted
function encodeBasic(username, password) {
utf8bytes = new TextEncoder().encode(username + ":" + password);
binaryString = String.fromCodePoint(...utf8bytes);
return btoa(binaryString);
}
function decodeBasic(base64String) {
binaryString = atob(base64String);
utf8bytes = Uint8Array.from(binaryString, (c) => c.codePointAt(0));
both = new TextDecoder().decode(utf8bytes);
seperator = both.indexOf(':');
return [both.slice(0,seperator), both.slice(seperator+1)];
}HTTP Basic Auth
- Cannot customize username/password prompt
- Browser will remember to keep sending auth
- All files and subdirs at or below will be considered authenticated
- If we authenticate at
/stuff/private/index.html: /stuff/private/1browser will assume is authenticated/stuff/private/folder/banana.htmlbrowser will assume is authenticated
- If we authenticate at
HTTP Basic Authentication
HTTP Digest Auth
- Defined in RFC 2069, Franks et al, 1997.
- Uses cryptographic hashes, designed to hide username & password...
- But it uses MD5 which is broken.
- Secure SHA-256 hash added only in 2021 (firefox) and 2023 (chrome)
- So... You must use another encryption layer (TLS) below HTTP (HTTPS) for security!
- Not really used...
HTTP Digest Auth
- Doesn't prevent tampering with content, headers, paths, ...
- Just use TLS!
Session Cookie Authentication
Signed Token Authentication
Signed Token Authentication
- Response:
401 Unauthorized&WWW-Authenticate: Bearerheader. - Request:
Authorization: Bearerheader - Can use
Set-CookieandCookieto transfer token- But... it can be tripped up by CORS rules!
Access-Control-Allow-Origin:and friends.
JSON Web Tokens
{
"alg": "HS256",
"typ": "JWT"
}{
"sub": "user_id=1234567890",
"custom": "whatever",
"iat": 1698689742
}- Base64 Encoded + "." + Base64 cryptographic signature
The OAuths
- Allows a user to tell authorization server it's ok to allow a client (which can be a server) to access resource server API on their behalf.
- Example: User allows their email application to access gmail on their behalf.
- Client: email application
- Authorization server: accounts.google.com
- Resource server: gmail.com
The OAuths
- Allows a user to tell authorization server it's ok to allow a client (which can be a server) to access resource server API on their behalf.
- Example: User allows their email application to access gmail on their behalf.
- Client: super powered mail manager service $100/month guaranteed success (also a website/server, actually)
- Authorization server: accounts.google.com
- Resource server: gmail.com
OAuth 1
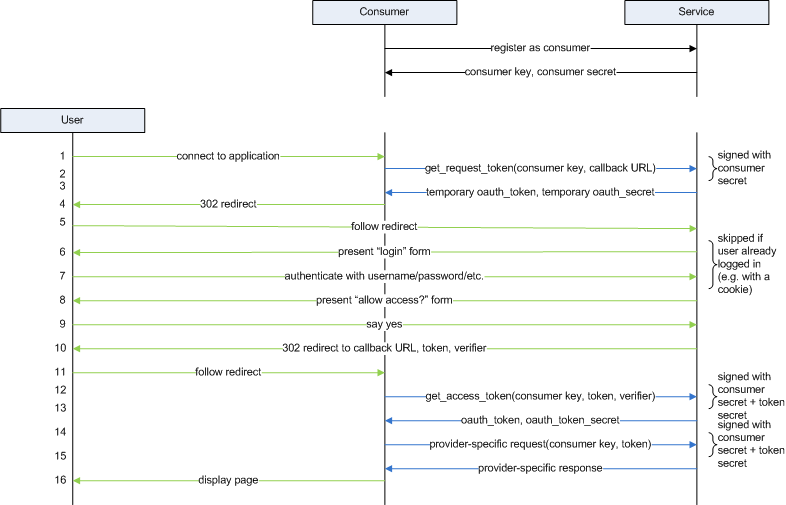 https://commandlinefanatic.com/cgi-bin/showarticle.cgi?article=art014 Joshua Davies, 2012
https://commandlinefanatic.com/cgi-bin/showarticle.cgi?article=art014 Joshua Davies, 2012
OAuth 2
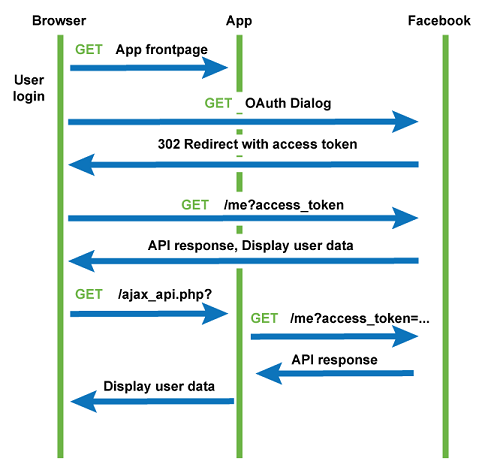 https://www.soapui.org/docs/oauth2/oauth2-overview/ Smartbear Software, 2023
https://www.soapui.org/docs/oauth2/oauth2-overview/ Smartbear Software, 2023
OAuth 1 vs 2
- More complicated
- More secure
- Slower
- Should be used over TLS
- RFC 5849
- Easier to implement
- Less secure
- Faster (fewer steps)
- Must be used over TLS
- RFC 6749
OpenID Connect
- Do OAuth 2.0
- The site you are logging into is the client, AKA Relying Party (RP).
- The site you are logging in with is the authorization server and resource server, AKA Identity Provider (IDP).
-
Use OAuth 2.0 authorization to get a JWT from the IDP, which we then give to the RP as proof of who we are.
- The thing we are AUTHORIZING the client/RP to do is request information about who we are, according to the IDP/authorization server.
OpenID Connect
SAML
- Like OpenID Connect but doesn't use OAuth or JWT, instead uses XML and its own thing
- Mostly used by academic institutions (such as the University of Alberta)
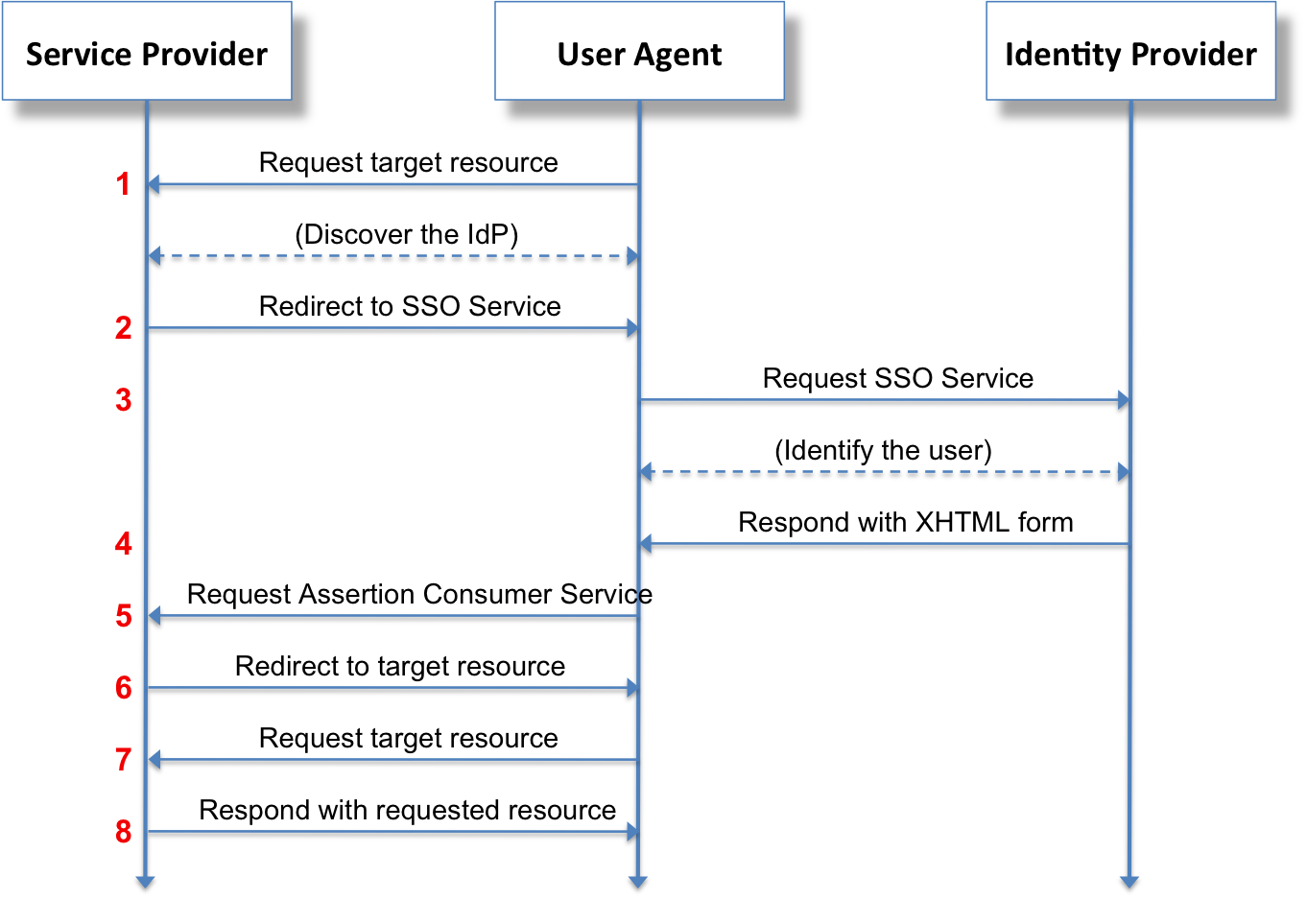 https://commons.wikimedia.org/wiki/File:Saml2-browser-sso-redirect-post.png Ayungn, 2021, Wikimedia Commons
https://commons.wikimedia.org/wiki/File:Saml2-browser-sso-redirect-post.png Ayungn, 2021, Wikimedia Commons
Cookie: vs Authorization: Bearer
- Both headers sent by the client
- Automatically sent by browser
- Can run afoul of CORS rules
- Less control by your code
- Only sent with AJAX when specified
- Less likely to run afoul of CORS rules
- Requires more code to use
License
Copyright 2014-2023 ⓒ Abram Hindle
Copyright 2019-2023 ⓒ Hazel Victoria Campbell and contributors

The textual components and original images of this slide deck are placed under the Creative Commons is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
Other images used under fair use and copyright their copyright holders.
License
Copyright (C) 2019-2023 Hazel Victoria Campbell
Copyright (C) 2014-2023 Abram Hindle and contributors
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal
in the Software without restriction, including without limitation the rights
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
copies of the Software, and to permit persons to whom the Software is
furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in
all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN.
01234567890123456789012345678901234567890123456789012345678901234567890123456789